Description
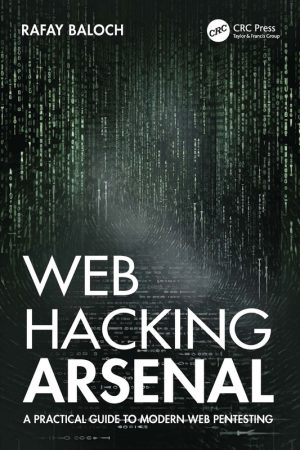
Advanced Web Hacking Course
Advanced Web Hacking Mastery is your gateway to mastering modern penetration testing techniques, ethical hacking strategies, and real-world web security skills for high-demand cybersecurity careers.
In today’s digital world, businesses rely heavily on web applications; therefore, securing them has become more important than ever. This Advanced Web Hacking Course equips you with practical knowledge and hands-on skills to identify, exploit, and mitigate vulnerabilities. Moreover, you will learn how hackers think, which allows you to defend systems more effectively. As a result, this course is ideal for aspiring ethical hackers, cybersecurity professionals, and IT enthusiasts.
Why Choose This Course?
First of all, this course focuses on real-world scenarios rather than just theory. In addition, you will work with modern tools and techniques used by professionals. Furthermore, the course structure ensures progressive learning, so you can build expertise step by step. Consequently, even beginners can advance to professional-level skills with consistent practice.
What You Will Learn
- Understand web application architecture and security fundamentals
- Identify vulnerabilities such as SQL Injection, XSS, CSRF, and more
- Perform advanced penetration testing techniques
- Use tools like Burp Suite, Metasploit, and Nmap effectively
- Exploit authentication and session management flaws
- Secure applications by applying best practices
Course Modules
To begin with, you will explore the basics of web security and HTTP protocols. Next, you will dive into vulnerability analysis and exploitation techniques. After that, the course covers advanced topics such as privilege escalation and bypassing security mechanisms. Finally, you will learn reporting and remediation strategies, which are essential for professional ethical hackers.
Who Should Enroll?
This course is perfect for students, IT professionals, and cybersecurity enthusiasts. Additionally, developers who want to secure their applications will benefit greatly. Even if you are preparing for certifications, this course will strengthen your practical knowledge significantly.
Career Opportunities
After completing this course, you can pursue roles such as Ethical Hacker, Penetration Tester, Security Analyst, or Bug Bounty Hunter. Furthermore, companies actively seek professionals with these skills, so your career opportunities will expand rapidly.
Explore These Valuable Resources
- OWASP Top 10 Web Security Risks
- Web Security Academy by PortSwigger
- National Vulnerability Database (NVD)
Explore Related Courses
- Explore Related Courses
- Explore Related Courses
- Explore Related Courses
- Explore Related Courses
- Explore Related Courses
Conclusion
In conclusion, this Advanced Web Hacking Course provides everything you need to succeed in cybersecurity. Not only will you gain technical expertise, but you will also develop a hacker mindset. Therefore, if you want to build a high-paying career in cybersecurity, this course is the perfect starting point. Start learning today and take your skills to the next level.















Reviews
There are no reviews yet.